Signature based volatile memory forensics: a detection based approach for analyzing sophisticated cyber attacks | SpringerLink

Practical Memory Forensics: Jumpstart effective forensic analysis of volatile memory: Ostrovskaya, Svetlana, Skulkin, Oleg: 9781801070331: Amazon.com: Books
The Art of Memory Forensics: Detecting Malware and Threats in Windows, Linux, and Mac Memory | Wiley




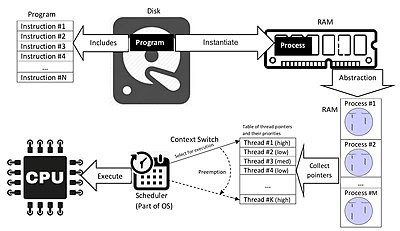
![PDF] Memory Forensics: Review of Acquisition and Analysis Techniques | Semantic Scholar PDF] Memory Forensics: Review of Acquisition and Analysis Techniques | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5844da2c4456091748958bcc035ff8a52e6d8340/18-Figure1-1.png)